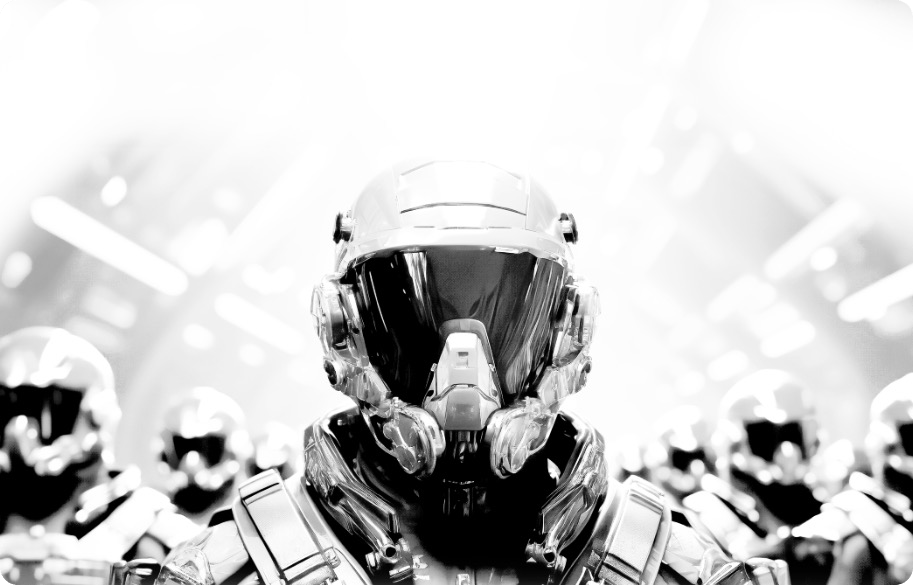
Understanding Today's Cyber Threat Landscape
The Dynamics of Threat Collaboration
As different threat actors weave their networks more tightly, a new pattern emerges. The CaaS economy facilitates a space where cyber attackers don’t need to create their tools – they can purchase them, have them customized, and even receive support services – all from the hidden recesses of the dark web.
For businesses, this signifies a change in the cyber game. The ease of access to malicious tools and services means threats emerge faster and fiercer. It becomes crucial for modern defenders to unravel the intricate network linking nation-state actors, organized cyber gangs, and individual hackers.
Inside the Cybercrime Hub - The Dark Web
The dark web, while a sanctuary for anonymity and freedom, has also morphed into a hub for cybercriminals. While services like TOR, I2P, or Hyphanet offer legitimate uses, they've undoubtedly opened the gates for heightened cyber criminal activities. This dark ecosystem has augmented the scale and intricacy of cyber threats, making them more formidable than ever.
From Crime to Commodity: The Role of Initial Access Brokers (IABs)
Data breaches have become a marketplace, thanks to the rise of IABs. Acting as intermediaries, they peddle unauthorized access to compromised systems. By trading in stolen credentials and software vulnerabilities, they have commodified cyber threats, paving the way for swifter and more vicious cyber onslaughts.
Cyber Affiliates: Redefining Collaborative Threats
The era of solitary cyber attackers is phasing out, making way for collaborative threats orchestrated by cyber affiliates. These experts collaborate on cyber attacks for a share of the spoils. Their role in expanding the ransomware-as-a-service (RaaS) frameworks is significant, intensifying the threat landscape and ensuring the malicious gains are multiplied.
Behind the Veil: The Silent Enablers
Deep within the maze of cybercrime are the silent orchestrators. Whether it's crypter developers masking malware or bulletproof hosting providers offering a sanctuary, these silent partners facilitate a smoother execution of cyber threats.
The Role of Cryptocurrency in Modern-Day Threats
Cryptocurrencies have emerged as the preferred medium for cybercriminal transactions. Decentralized, hard-to-trace, and versatile, they play a pivotal role in the cyber threat landscape.
Looking Ahead
As the interdependence among cybercriminals becomes more pronounced, businesses must develop holistic cybersecurity strategies. At Reveald, our commitment is unwavering. We're here to ensure you're fortified against every gradient of cyber threat. For an in-depth understanding and to bolster your defenses, connect with Reveald today.
The force multiplier for security teams.
Welcome to the new age of predictive cybersecurity.
Leverage the power of AI to discover and prioritize cybersecurity risks, vulnerabilities and misconfigurations across your entire environment