Safeguarding
Mergers & Acquisitions
Transforming the M&A due diligence process using data-driven assessments and proactive remediation strategies.

Transforming the M&A due diligence process using data-driven assessments and proactive remediation strategies.
A not-for-profit healthcare organization (HCO) has been caring for local communities since the founding of its first hospital in the late 1800’s. With more than 20,000 team members, including employees, providers, and volunteers, the HCO has grown from its original one-hospital organization into a large not-for-profit community-based, locally owned health care system. The HCO’s comprehensive system of healthcare serves patients in multiple cities and includes numerous inpatient care, primary care, virtual care, urgent care, and dedicated pediatric care and specialty services in over ten hospitals. It also includes affiliated physicians and medical associates and a wide range of community outreach programs in cities where it has a presence.
Reveald used the Epiphany Intelligence Platform to provide the HCO with adversarial assessments to provide information about the HCO’s security status. Based on the positive results of the HCO’s initial adversarial assessment, the HCO asked Reveald to perform an adversarial assessment on a hospital it was acquiring in order to understand its security posture prior to the acquisition.
Reveald performed an adversarial assessment of a not-for-profit healthcare organization’s (HCO) security posture using the Epiphany Intelligence Platform. The HCO was extremely happy with the information provided by the adversarial assessment and the guidance it provided to remediate potential security risks.
Moving forward, the HCO was acquiring a hospital to add to its portfolio of healthcare facilities. As part of integrating the hospital into their organization’s environment, they wanted to understand the hospital’s potential attack surface and inherent risks and they wanted to understand the risks of the new environment before bringing it into the HCO’s clean environment.
The HCO needed to meet regulatory requirements and wanted to understand what security and compliance remediation they needed to do to have a secure integration. In the post-merger haste to integrate, security can be forgotten about, which can lead to active attackers having a path in to the acquiring organization’s critical resources. It was essential for the HCO to avoid this.
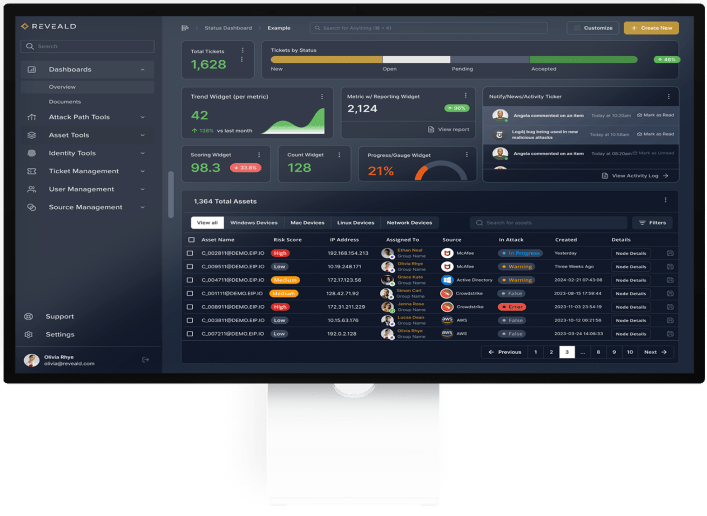
Security is an important part of a successful merger. Reveald uses the Epiphany Intelligence Platform to provide guidance supporting due diligence, final terms, and integration in a merger and acquisition.
Reveald can help at every phase of technical due diligence prior to an acquisition. Understanding the attack surface, defensive posture, and exploitability of the infrastructure an organization is potentially acquiring is essential. Having visibility into these things can minimize unwanted surprises during integration, and it can prevent the core business network from inadvertently being exposed to attack paths within an acquired organization.
To assess an acquisition target, data can be uploaded from the target organization’s security and IT assessment tools when the Reveald team is onsite, or the target organization can simply export and upload data to Reveald.
Once Reveald has the data, it begins to build and analyze potential attack paths within the target organization. This information can be used to understand the potential costs to remediate those paths and bring the target network up to the acquiring organization’s security standards.
Using the Epiphany Intelligence Platform, Reveald can also highlight where the target company may have operational failures in its configuration management, vulnerability management, or identity management by surfacing those issues through the target organization’s own data sources.
Using the technical information provided by the Epiphany Intelligence Platform, an organization can account for the cost of reducing exposure of the target organization’s critical business objects. An acquiring organization can also understand the amount of effort required—from a time-and-materials perspective—to bring the target organization into alignment with existing policies. This provides the opportunity to capitalize remediation and be proactive in integration planning, instead of reacting to new problems discovered later during the integration of the target company.

Integration is a critical phase to complete an acquisition. It’s also the one where most hidden costs are found. While it’s potentially easy to account for and integrate processes and workflow, it’s much harder to understand the effort needed to safely integrate and secure a once-remote network.
Traditionally this is achieved by putting a firewall between networks and methodically opening one service at a time to the remote environment. This process can take many months or even years in larger acquisitions and often results in misconfigurations and over-permissioning. The Epiphany Intelligence Platform can accelerate this by showing which services are safe to integrate without generating attack paths.
Epiphany uses its attack path knowledge and its awareness of the most critical exploitable conditions in both networks to guide the integration process, ensuring no inadvertent exploitable paths are created. Epiphany can use its data processing power to merge large complex data sets within both organizations’ IT and security tools to track the progress of major high-risk projects such as identity and access granting, endpoint protection migration, firewall configuration changes, vulnerability reduction, and more.
Based on their pre-merger concerns as well as the success of the previous adversarial assessment performed by Reveald, the HCO engaged Reveald to use the Epiphany Intelligence Platform to perform an adversarial assessment of the target hospital. The assessment analyzed over 6,000 users and over 8,000 devices.
Key areas of evaluation were:
Epiphany uncovered many issues for the HCO to address prior to the merger, ensuring that their systems weren’t impacted by new attack paths unintentionally introduced by the target hospital. Epiphany identified that the target hospital had poor security practices, including poor vulnerability management and permissions management. Additionally, Epiphany identified numerous non-admin users who had the ability to use remote desktop protocol (RDP) to directly access domain controllers. There were also a number of high-value identities logging into areas where they shouldn’t be. And there were several attack paths leading into high value roles.
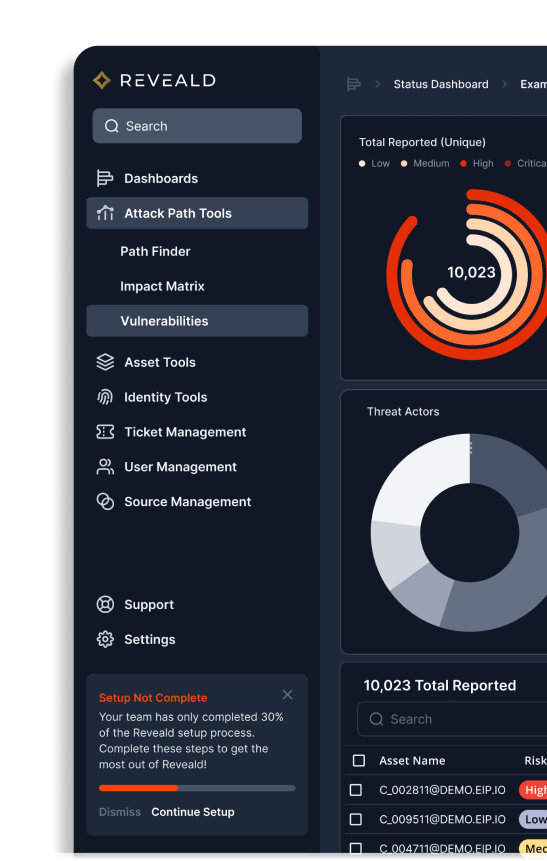
Other findings included:
If your organization is embarking on an M & A journey, Reveald and the Epiphany Intelligence Platform are with you every step of the way, from the moment your tech team arrives to assess a target organization through the day your systems are fully-merged.
Reveald’s Continuous Exposure Management 360° (CEM360°) service leverages the Epiphany Intelligence Platform coupled with expert analysts from the Reveald Fusion Center to provide 24x7 cybersecurity vulnerability prioritization based on advanced attack graph analysis. This leads to business risk reduction through data integration and automated security analysis, validation, reporting, and guided resolution.
Reveald’s experts work in partnership with its clients’ teams to prioritize issues that are most likely to cause cybersecurity events across identity, configuration, and defensive controls. They continuously manage and tune the Epiphany Intelligence Platform, ensuring integrations with cybersecurity toolchains work flawlessly to generate the most valuable remediation information.
The CEM360° service includes full support for the implementation of a unique Epiphany Intelligence Platform instance, training for a client’s teams, reporting on business objective results, risk minimization, and continuous vulnerability prioritization updates.